GitLab CI
You can use Phase to sync secrets to GitLab CI Variables.
When secret syncing is enabled, secrets stored inside Phase will be treated as the source of truth. Any secrets on the target service will be overwritten or deleted. Please import your secrets into Phase before continuing.
Prerequisites
- Sign up for the Phase Console and create an App.
- Enable Server-side Encryption (SSE) for the App from the Settings tab.
Step 1: Authenticate with GitLab
Token Types for Authentication
You can use two types of tokens to authenticate Phase with GitLab: Personal Access Token (PAT) and Group Access Token.
Personal Access Token (PAT)
A Personal Access Token (PAT) is tied to an individual user's GitLab account. While this can be convenient for personal projects, it has some significant drawbacks:
- User Dependency: If the user who created the PAT is removed from a group or deletes their account, the integration using that token will break.
- Scope Limitation: The token's permissions are limited to the user's access level.
Group Access Token (GAT)
A Group Access Token is associated with a GitLab group rather than an individual user. This method is more robust for team and organizational use:
- Resilience: The token remains valid as long as the group exists, regardless of changes to individual user accounts.
- Consistent Access: All members of the group can use the token for authentication, ensuring continuous integration.
Availability of Group Access Tokens
- GitLab.com: Group access tokens are available for users with the Premium or Ultimate license tiers. They are not available with a trial license.
- GitLab Dedicated and Self-Managed Instances: Group access tokens are available with any license tier.
Given these factors, it is recommended to use Group Access Tokens for authenticating Phase with GitLab to ensure stable and continuous integration, especially in team or organizational environments.
Create a Personal Access Token (PAT)
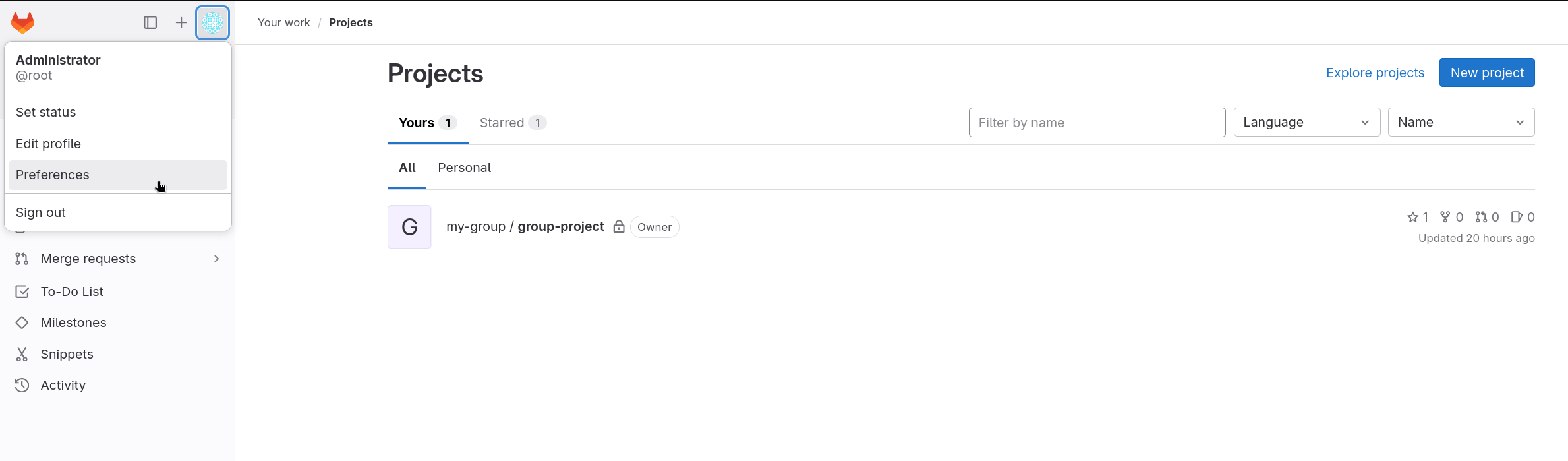
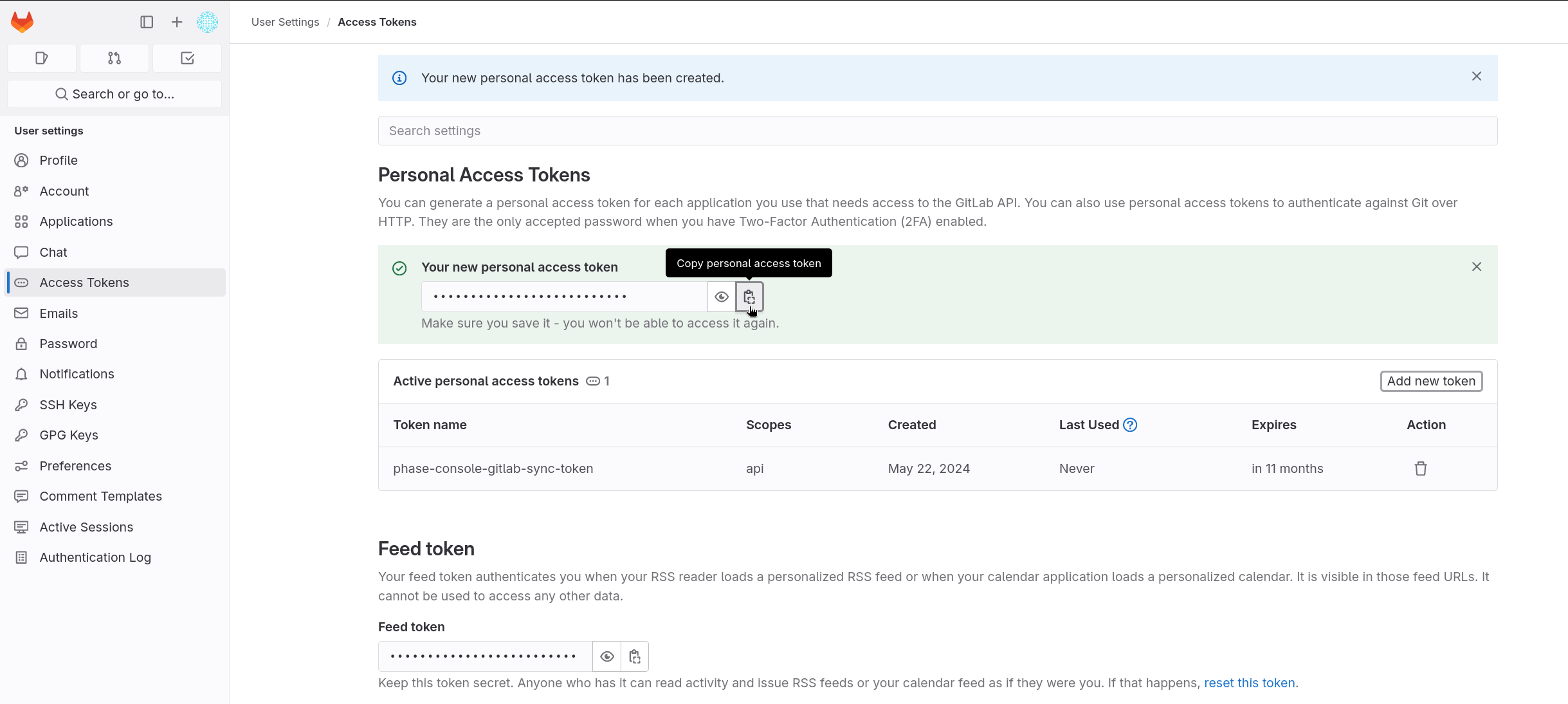
- Go to User Settings from the sidebar and click on Access Tokens.
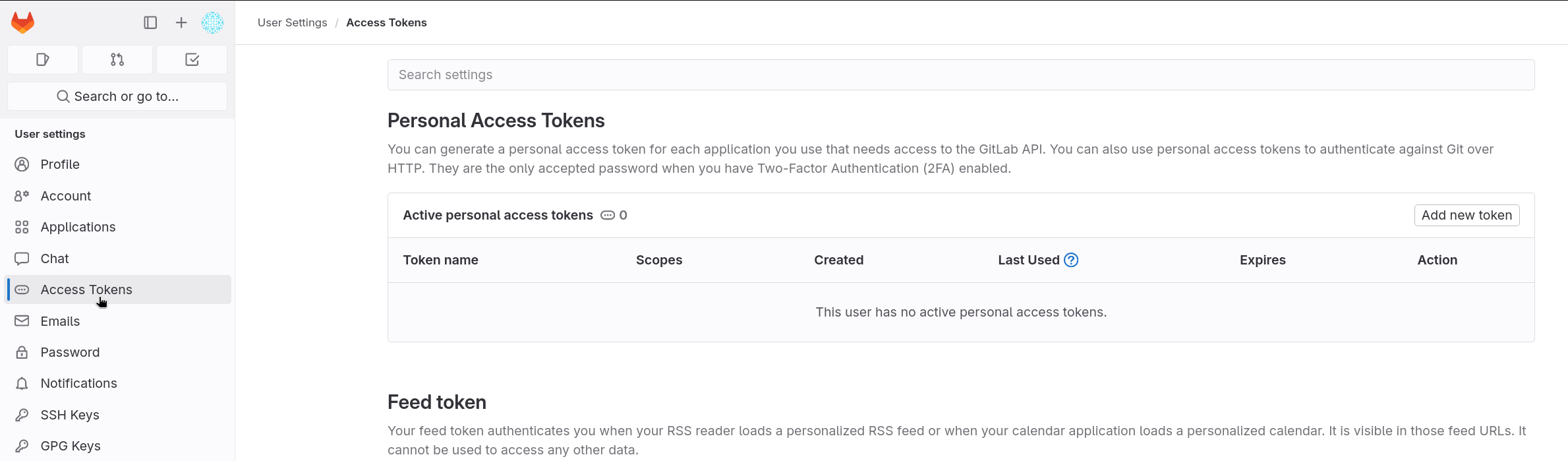
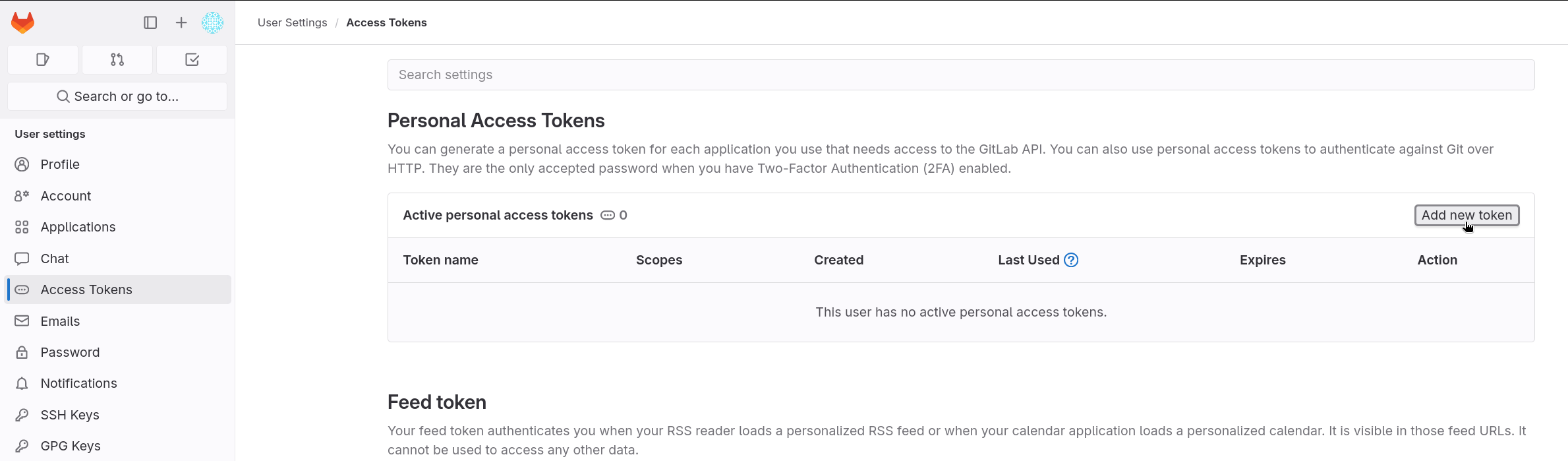
- Click on Add new token.
- Fill in the Token name, set the
apiScope, and set the Expiration date.
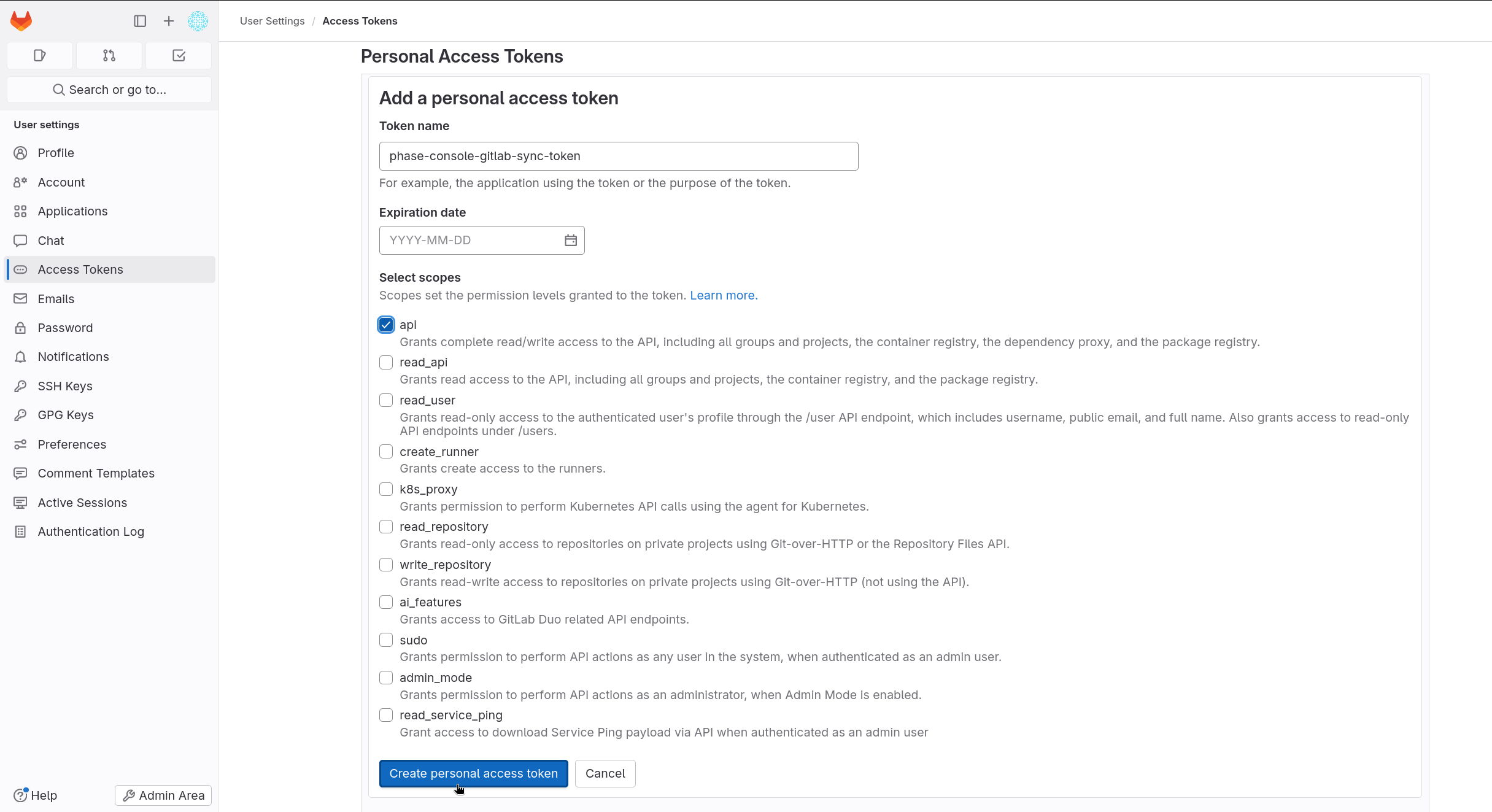
If you leave the Expiration date blank, GitLab will create a token with a
12-month expiry by default. Ensure you set an appropriate expiration date to
prevent the token from expiring unexpectedly. Also, ensure the api scope is
selected to allow necessary permissions for Phase integration.
- Click Create personal access token and copy the token.
Create a Group Access Token (GAT)
This feature is only available on GitLab if you have the Premium or Ultimate license tier. Group access tokens are not available with a trial license. On GitLab Dedicated and self-managed instances, you can use group access tokens with any license tier.
- Go to your GitLab Group.
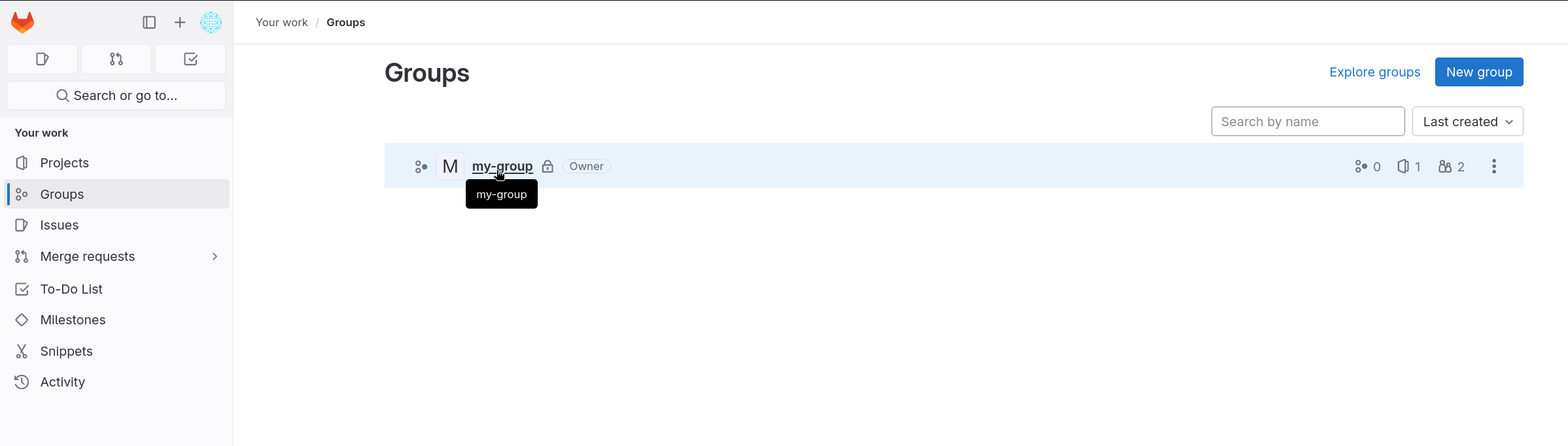
- Navigate to Settings > Access Tokens.
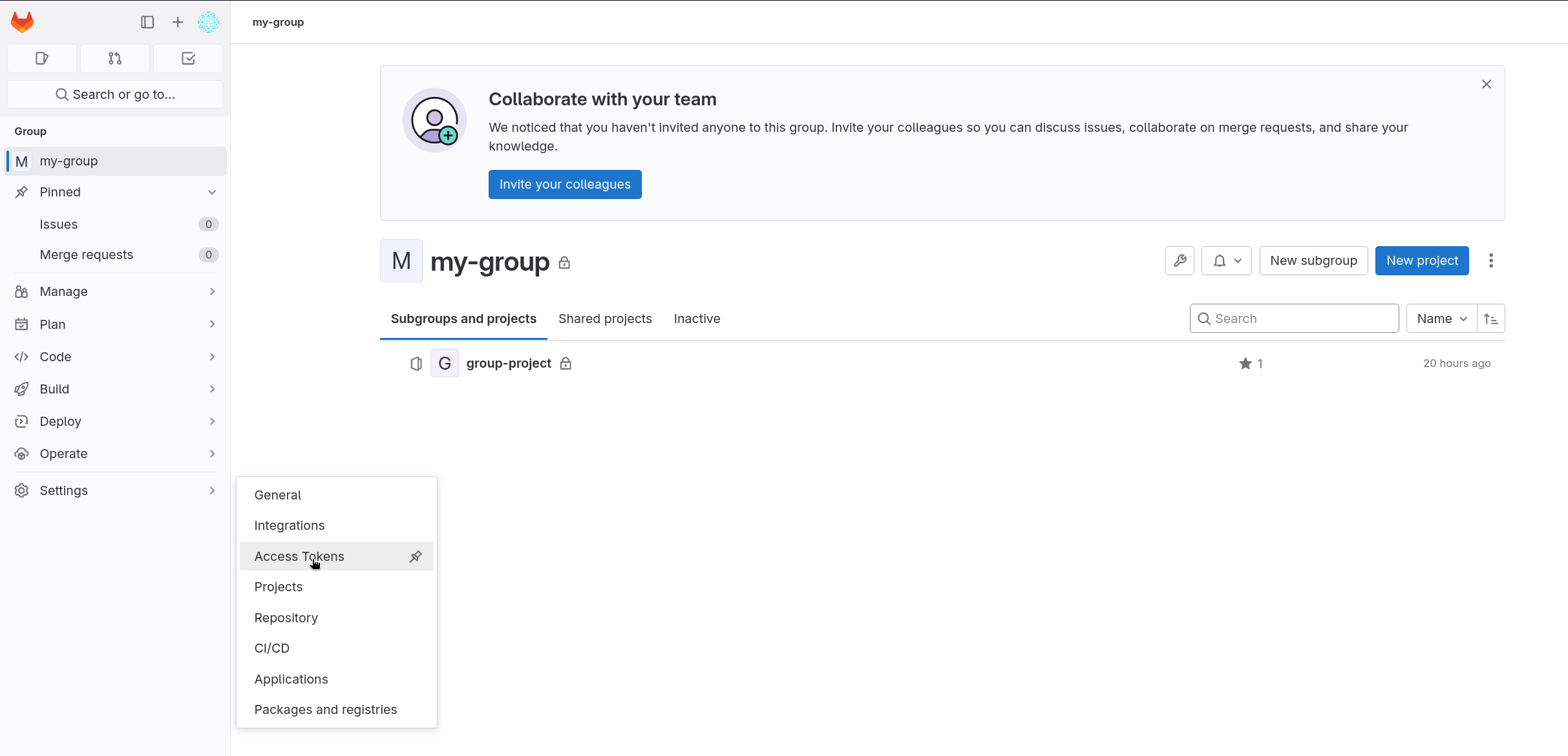
- Click on Add new token.
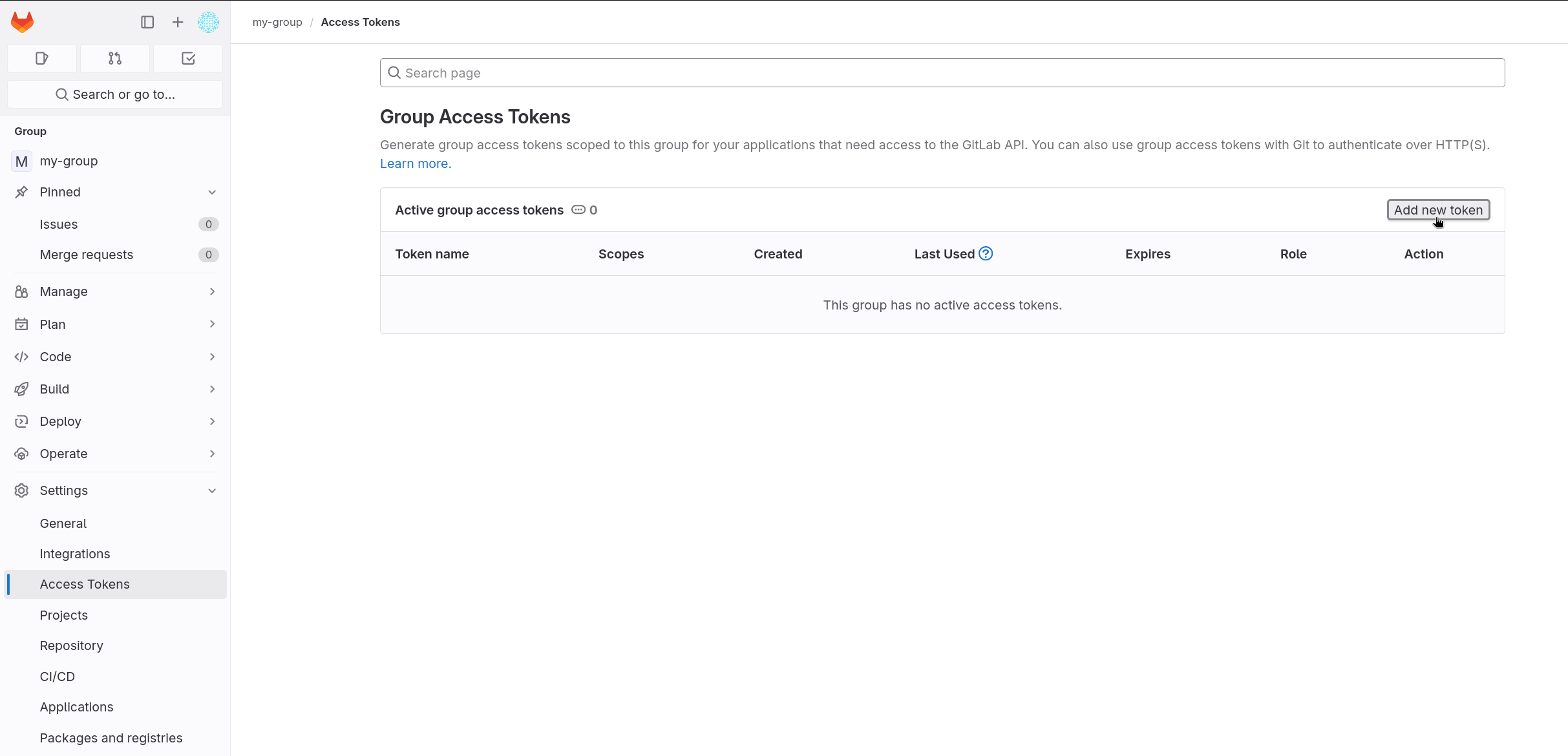
- Fill in the Token name, select the
OwnerRole, set theapiScope, and set the Expiration date.
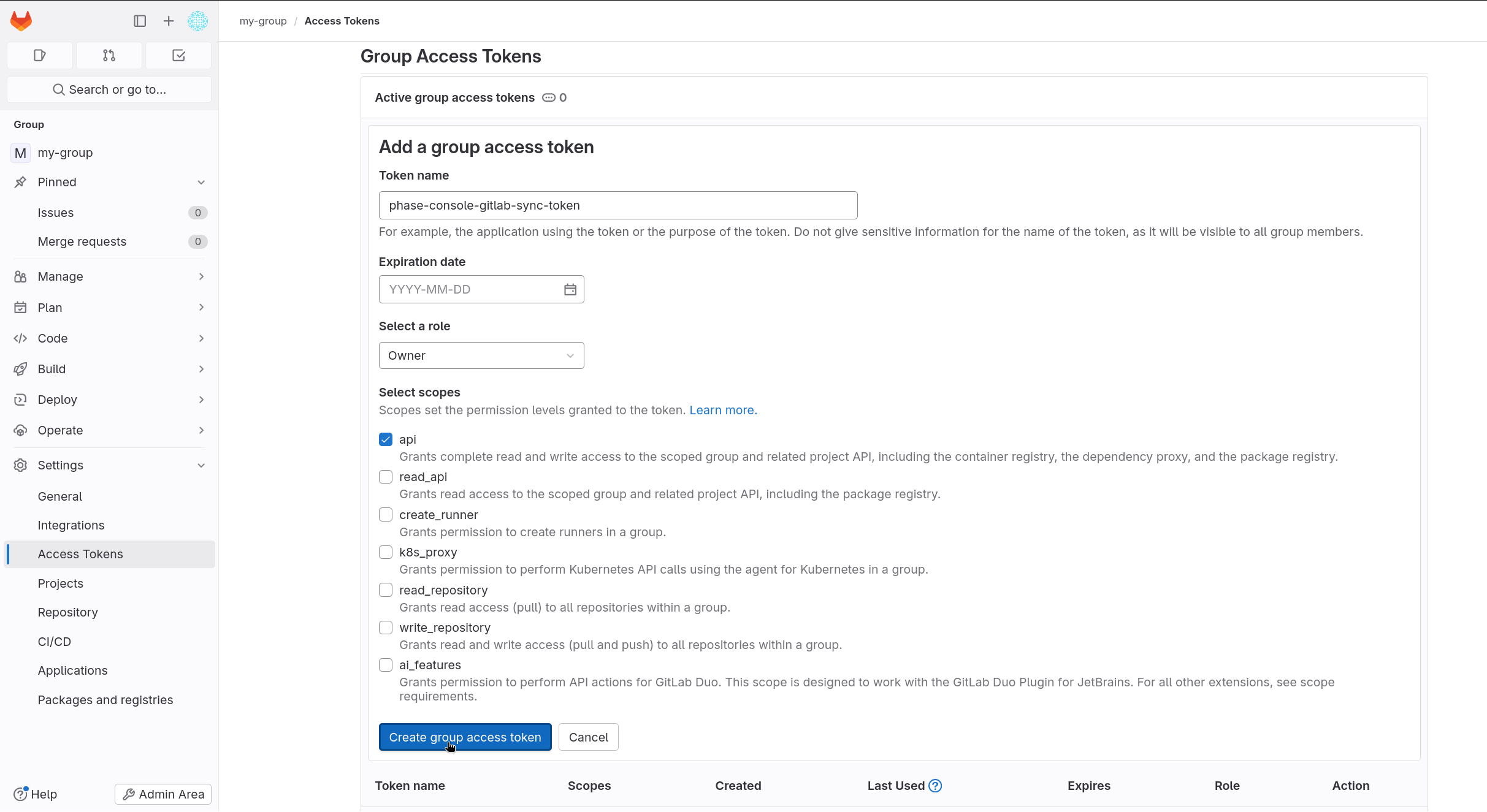
If you leave the Expiration date blank, GitLab will create a token with a
12-month expiry by default. Ensure you set an appropriate expiration date to
prevent the token from expiring unexpectedly. Also, ensure the api scope is
selected to allow necessary permissions for Phase integration.
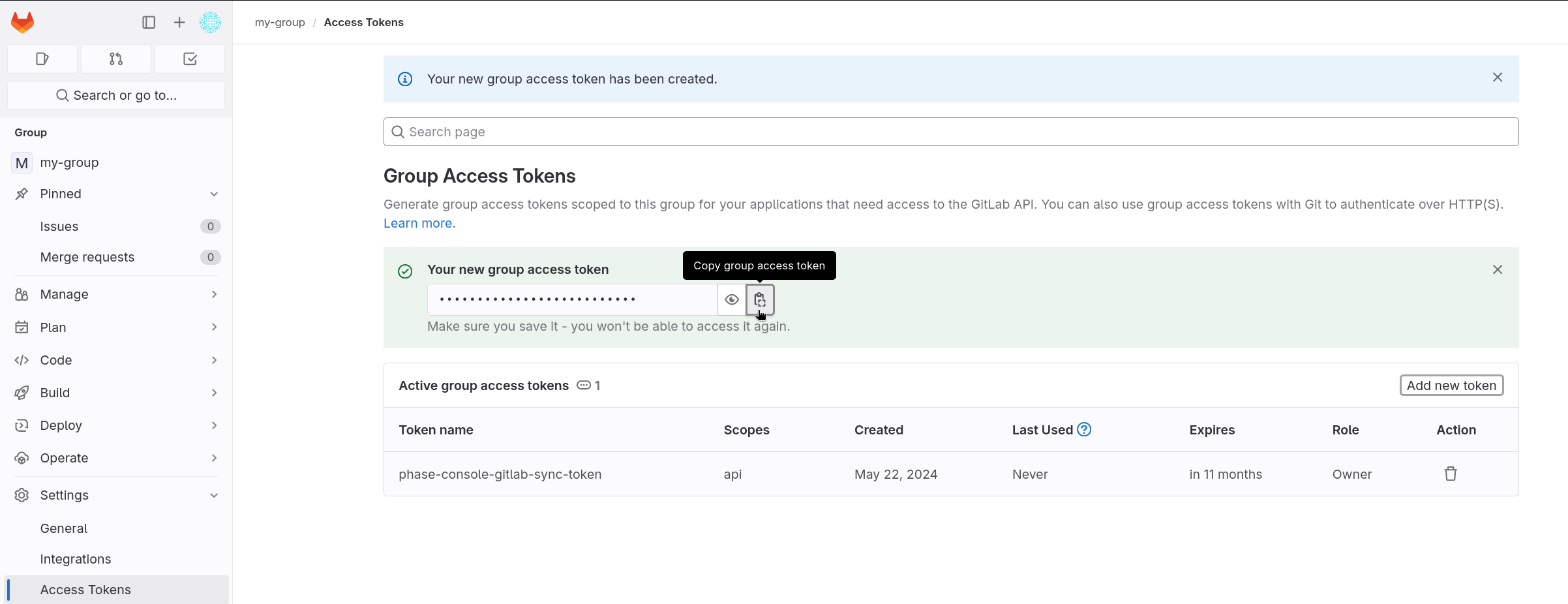
- Click Create group access token and copy the token.
Store authentication credentials in Phase
Your credentials are kept secure with robust application-layer encryption. Phase encrypts your credentials directly in the browser and only decrypts them in memory to perform sync operations. Your credentials are never stored in plaintext.
- Go to Integrations from the sidebar and click on Third-party credentials in the integrations tab.
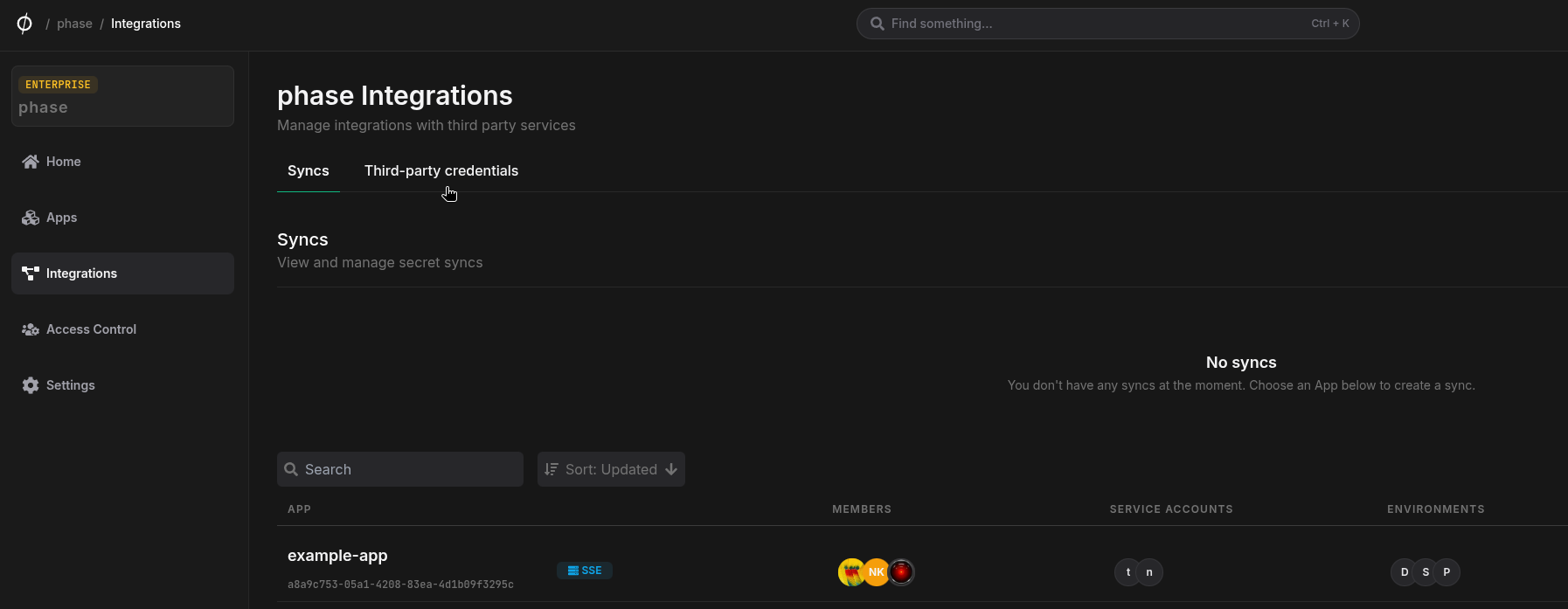
- Click on GitLab
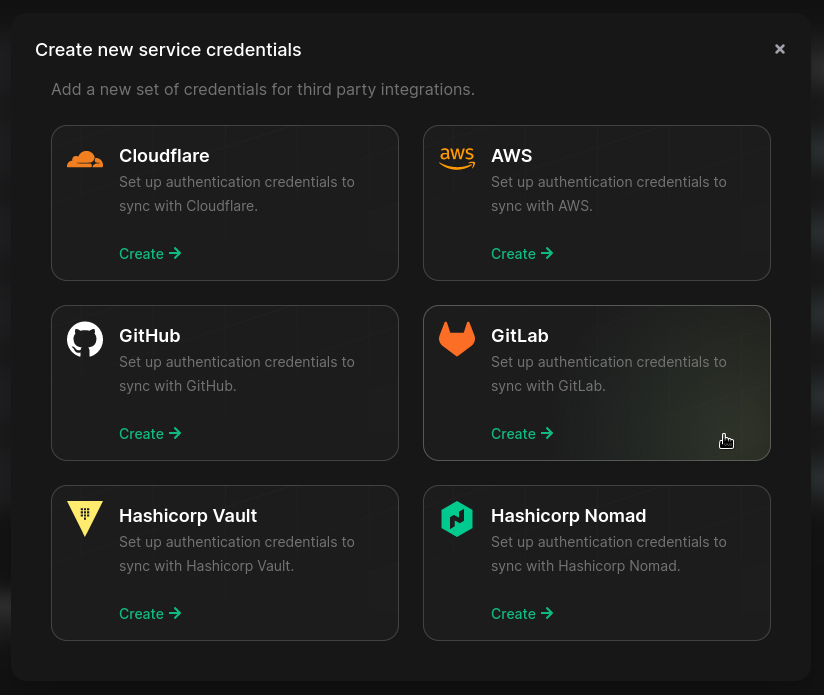
- Enter your GitLab instance host (use
https://gitlab.comfor GitLab.com) and token. Enter a descriptive name for these credentials and click Save
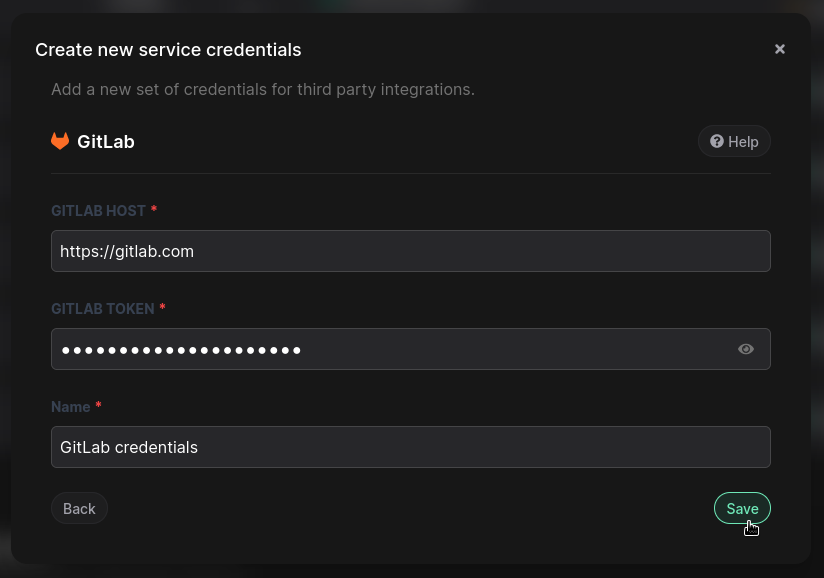
Your credentials will be encrypted and saved. You can view and manage these credentials under Service Credentials in the Integrations screen.
Step 2: Configure Sync
Now that you have authenticated with GitLab, you can configure syncs for your app.
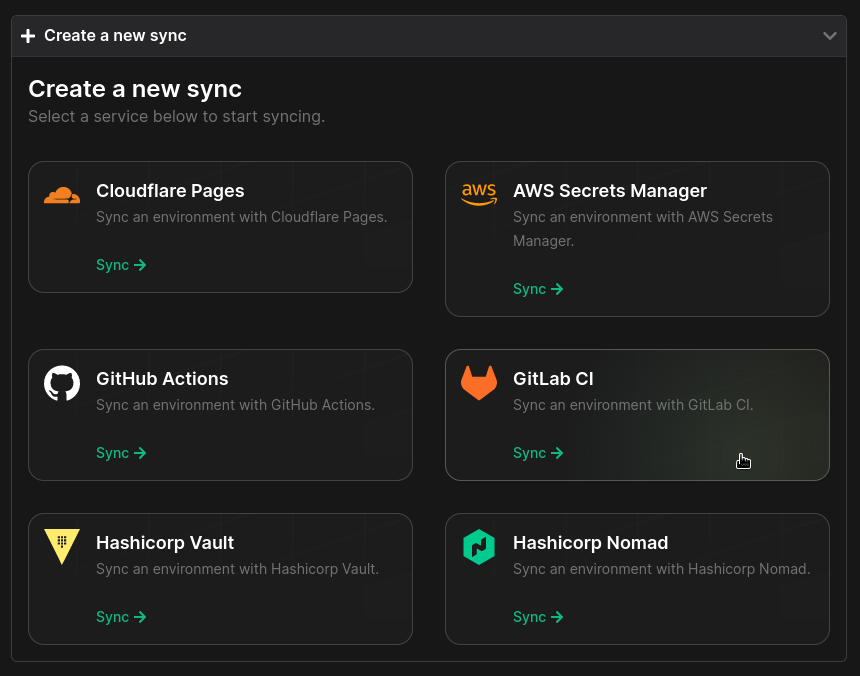
- Go to your App in the Phase Console and go to the Syncing tab. Select GitLab CI under the 'Create a new Sync' menu.
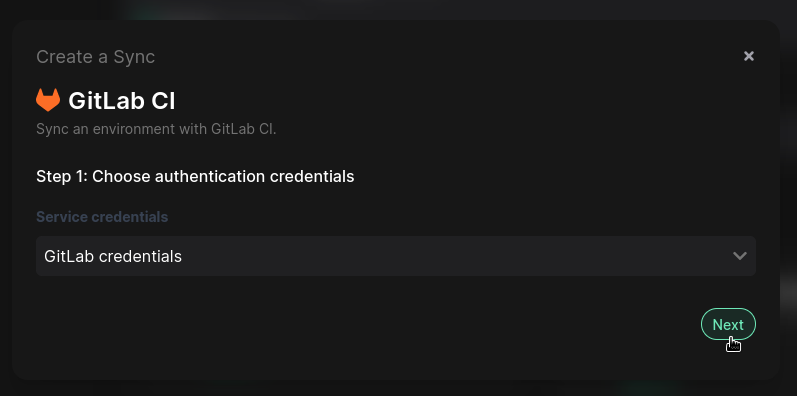
- Select the credentials stored in the previous step as the authentication method for this sync, and click Next.
-
Choose the source and destination to sync secrets. Select an Environment as the source for Secrets. Next, choose a GitLab Project or GitLab Group from the dropdown as the destination to sync Secrets to.
You can optionally also choose to mask and/or protect secrets synced to GitLab.
Masked variables must meet the following criteria in GitLab. If any secrets in the selected environment and path do not meet these requirements, the sync will fail.
Masked variables must:
- Be a single line.
- Be 8 characters or longer.
- Not match the name of an existing predefined or custom CI/CD variable.
Additionally, if variable expansion is enabled, the value can contain only:
- Characters from the Base64 alphabet (RFC4648).
- The @, :, ., or ~ characters.
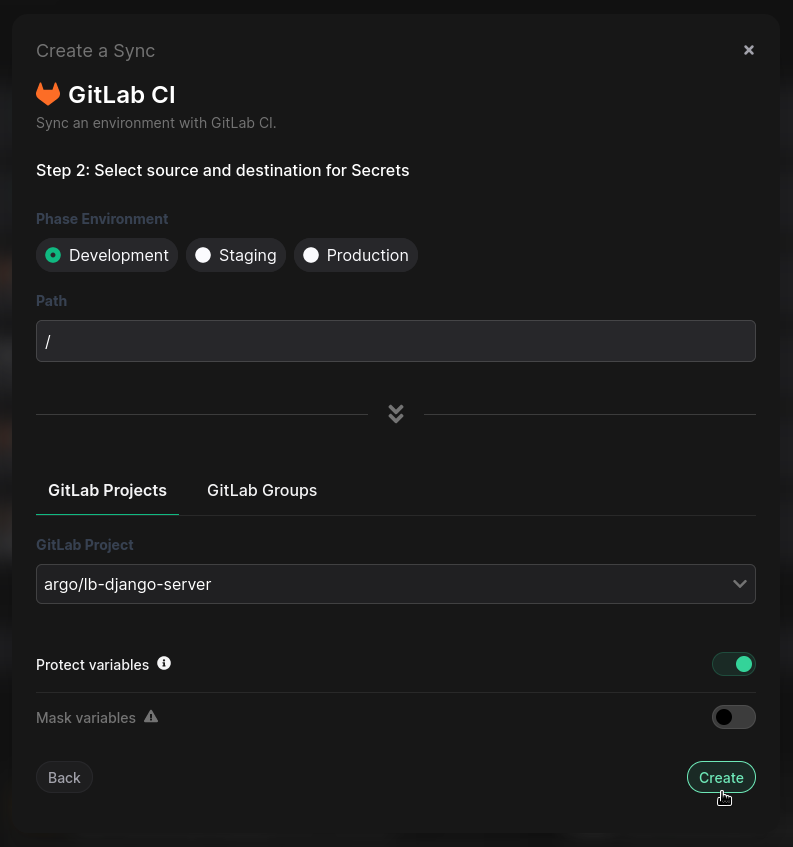
- Once you have selected your desired source and destination, click Create. The sync has been set up! Secrets will automatically be synced from your chosen Phase Environment to the GitLab Project or Group as CI/CD variables. You can click on the Manage button on the Sync card to view sync logs, pause syncing, or update authentication credentials.
Using the Phase CLI
Fetch secrets directly inside your GitLab CI pipeline during runtime without storing them in GitLab.
Prerequisites
- Sign up for the Phase Console and create an App.
PHASE_SERVICE_TOKEN
If you are using a Self-Hosted instance of the Phase Console, you may supply
PHASE_HOST environment variable with your URL (https://<HOST>).
For detailed CLI install options, please see: Installation
Setting PHASE_SERVICE_TOKEN:
- Navigate to your project in GitLab.
- Go to
Settings>CI/CD. - Under
Variables, click onExpand. - Click on
Add Variable. - Enter the key as
PHASE_SERVICE_TOKENand your secret as the value. Save it.
Example:
stages:
- prepare
- build_and_push
prepare_phase_cli:
stage: prepare
script:
- curl -fsSL https://pkg.phase.dev/install.sh | bash
- export $(phase secrets export --app "my application name" --env prod DOCKERHUB_USERNAME DOCKERHUB_TOKEN | xargs)
build_and_push_image:
stage: build_and_push
script:
- docker login -u $DOCKERHUB_USERNAME -p $DOCKERHUB_TOKEN
- docker build -t my-image .
- docker push my-image:latest
Using phasehq/cli Docker image:
stages:
- prepare
- build_and_push
prepare_phase_cli:
image: phasehq/cli
stage: prepare
script:
- secrets export --app "my application name" --env prod DOCKERHUB_USERNAME DOCKERHUB_TOKEN
artifacts:
untracked: true
build_and_push_image:
stage: build_and_push
script:
- docker login -u $DOCKERHUB_USERNAME -p $DOCKERHUB_TOKEN
- docker build -t my-image .
- docker push my-image:latest